Contents
As you might know, administrators have access via RDP enabled by default. They even don’t need to be members of Remote Desktop Users group for this.
But in some situations you may need to restrict remote access for a specific administrator. For instance, if you want to be sure that every task (backups for example), services or other stuff that may launch using his credentials won’t stop working.
So here is how to disable access through Remote Desktop (RDP) for the user with administrative privileges on Windows Server 2016 without disabling the user account itself.
How To Disable Remote Desktop Access (RDP) for the user with administrative privileges on Windows Server 2016 without disabling the user account itself
In such a way you can deny RDP access for any user who belongs to groups that have it – for instance, Administrators, Remote Desktop Users.
-
- Press Win+R.
- Type
secpol.mscand hit Enter: - Navigate to:
Security Settings\Local Policies\User Rights Assignment
- Double-click on Deny log on through Remote Desktop Services:
- Click Add User or Group:
- Click Advanced:
- Click Find Now:
- Select the user you want to deny access via Remote Desktop and click OK:
- Click OK here:
- Click OK again to save settings:
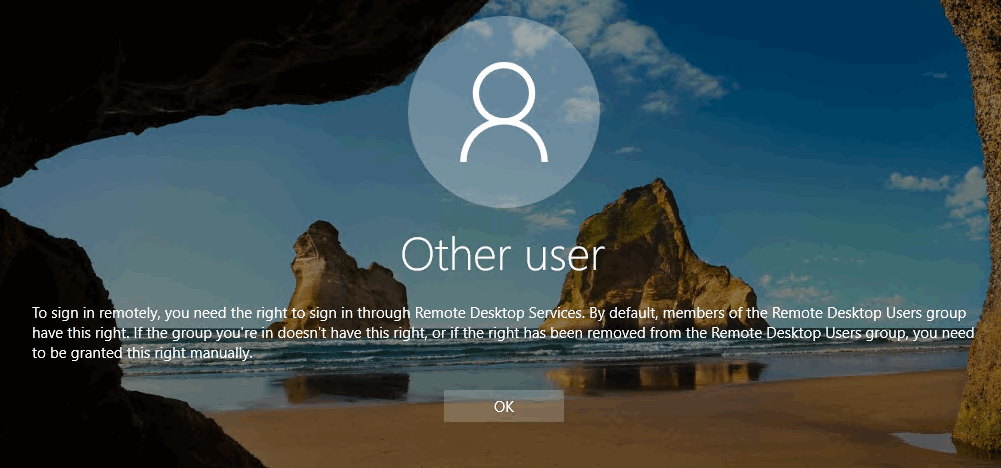
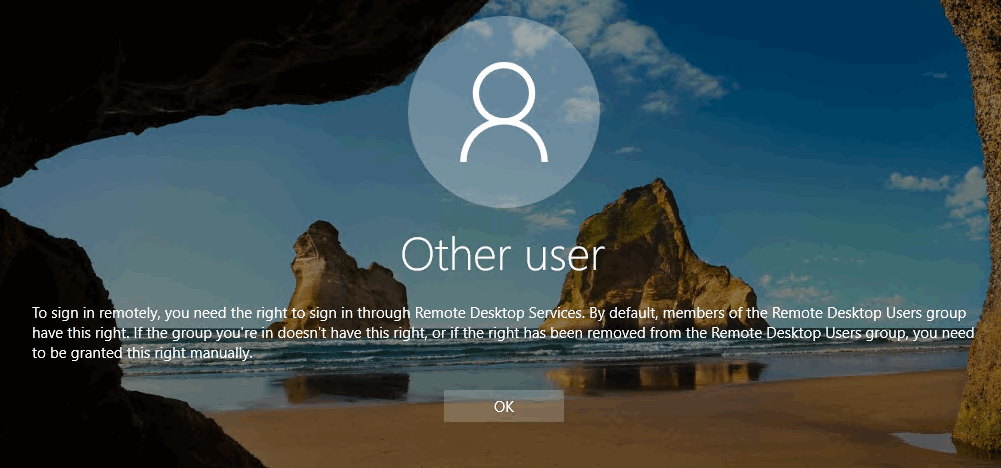
When blocked user will attempt to log in to Remote Desktop session he will see the message:
To sign in remotely, you need the right to sign in through Remote Desktop Services. By default, members of the Remote Desktop Users group have this right. If the group you’re in doesn’t have this right, or if the right has been removed from the Remote Desktop Users group, you need to be granted this right manually
How To Allow User To Access The Server Through Remote Desktop Again
If you want to allow a user from the Administrators group access RDP, all you need to do is open the Local Policy, remove the user from the list and click OK:
That’s it.









This option also gives the user to either Log Off or SHUT DOWN. Wow…this is brutal. A standard user can shut down a Server Computer.
Hi, my problem is my step mother. She has given someone remote access to her computer. He had convinced her to open a PayPal account that he had access to. We caught it just in time, changed her bank account numbers and solved that problem temporarily. I want to be able to remove remote access or password protect it so that she can’t open it to give this thief access again. He was able to steal $360.00. So far, all I see are ways to use remote access and no way to block it. Any suggestions?
Jim
First of all, we need to understand how exactly she provided access to her PC – via RDP or using some third-party program such as Teamviewer. The fact that you changed the PayPal password is good.
In case it turns out that you don’t know exactly how she given remote access, you should better do the following:
1. Look for third-party programs that provide remote access on that PC: TeamViewer, Anydesk, UVNC, Real VNC and uninstall them. On top of this, look for ‘Chrome Remote Desktop’ extension in the browser and remove it.
2. Turn off Microsoft Remote Desktop (RDP) and Remote Assistance. Press Win+[Pause/Break], click Advanced System Settings, go to Remote tab, disable RDP by selecting “Don’t allow remote connections”, then unset the checkbox “Allow Remote Assistance…” and click OK to save settings.
3. Scan your PC using Malwarebytes and remove all detected items.
4. Log in to your router settings and disable all port forwarding rules. If you don’t know how to do it, you can factory reset your router/modem (but you may need to configure Internet from a scratch).